CBS News Live
CBS News Texas: Local News, Weather & More
Watch CBS News





You can also expect lower humidity.

Dallas defenseman Miro Heiskanen scored two power-play goals, Roope Hintz had a goal and three assists and the Stars beat the Colorado Avalanche 5-3 in Game 2 on Thursday night to even the second-round Western Conference series.

Luka Doncic bounced back with 29 points, 10 rebounds and seven assists to help the Dallas Mavericks beat the Oklahoma City Thunder 119-110 on Thursday night and even the Western Conference semifinals at one win apiece.

Dallas police are examining security camera footage while detectives investigate.

The bill stalled earlier this week after senators from Virginia and Maryland objected to a provision that would allow an additional 10 flights a day to and from Ronald Reagan Washington National Airport.

The Biden administration announced a new regulation designed to allow immigration officials to deport migrants ineligible for U.S. asylum earlier in the process.

The organization is expanding its teachings to a diverse group of members.

Over the past several months, the CBS News Texas I-Team has reported on solar panel horror stories. This time, we set out to find a success story.

Instead of following traditional college paths, many are exploring alternative routes.

"Jesus was with me. He led me there."
Lucas Warren's birthday invitations went out last week for his fifth birthday party. There will be no party because he got killed in a flash flood Sunday morning.

CBS News Texas has new information from the Allen Police Department about its investigation into the outlet mall shooting that reveals for the first time the massive amount of manpower that responded to the scene.

Amazon is adding a new way to deliver ads through Prime Video. If you are in the ad-supported tier, Prime Video will start showing ads when you hit pause. It's part of the new interactive ad format, but you can avoid the commercials completely by paying an additional price per month.

There is a noticeable shift in post-grad choices for many high schoolers this year. In fact, many are embracing alternative routes as opposed to traditional college paths. And there's a surge of young adults entering trades or immediately starting their careers after high school.
An Australian study discovered blood tests can show changes in the level of two different antibodies, and those changes can identify which children will likely outgrow a peanut allergy without clinical intervention.

The Reauthorization Act would provide $105 billion for the Federal Aviation Administration and $733 million for the National Transportation Safety Board. The bill now heads to the House.
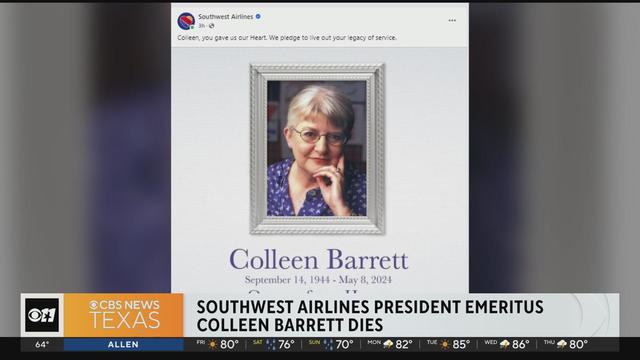
Southwest Airlines is mourning a woman that they call the heart and soul of their airline. Colleen Barrett has died at 79. Shee was considered instrumental in the carrier's early days, helping to bring about their love culture.

You can also expect lower humidity.
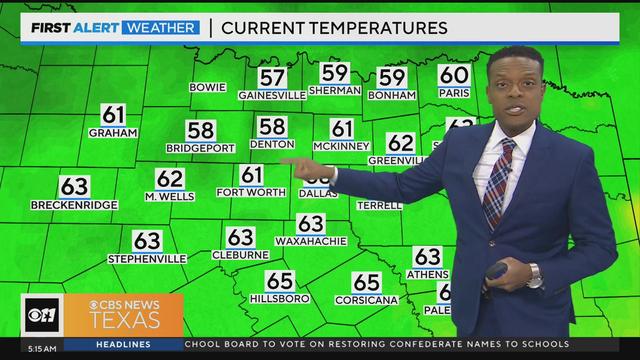
Friday will bring mostly sunny skies, with highs will be in the lower 80s.
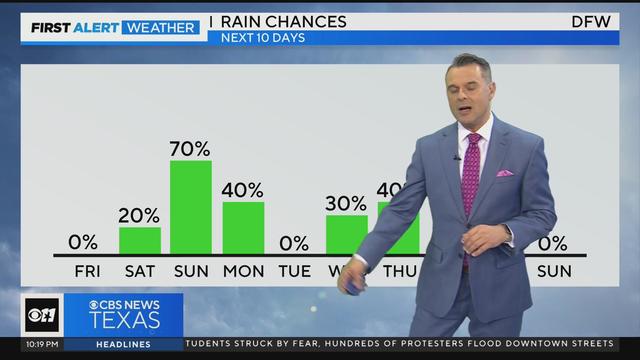
If you are hoping to get outside this weekend, Saturday is the better option as rain and a few storms return on Mother's Day.

Friday is the pick of the week with partly cloudy skies and highs in the lower 80s.

Over the past several months, the CBS News Texas I-Team has reported on solar panel horror stories. This time, we set out to find a success story.
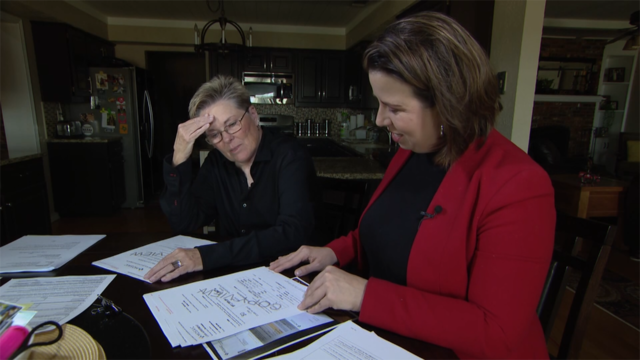
A Garland woman was surprised when she received a $97,000 bill for solar panels she doesn't have.

In a statement, Philips said it does not admit any wrongdoing but chose to settle "to end the uncertainty associated with litigation in the U.S."
A scammer a North Texas woman met on Instagram claimed to be a German cardiologist, and for months, the two messaged back and forth, building what she thought was a true relationship.

Texas police departments have the discretion to determine the frequency and extent of additional driving training for their officers. While some require driving training yearly or every other year, others do not.

Dallas-Fort Worth hockey fans are searching for anything and everything related to the Dallas Stars and the Stanley Cup Playoffs.

Dallas Trinity FC will play at the Cotton Bowl when the season begins in August.

The Olympic flame arrived in France aboard a 19th century tall ship to kick off a 7,500-mile journey to the Paris Summer Games.

Another professional women's sport is coming to town.

Stars goalie Jake Oettinger stopped 22 shots, ending his six-game streak of allowing two goals or less.

You can also expect lower humidity.

Dallas defenseman Miro Heiskanen scored two power-play goals, Roope Hintz had a goal and three assists and the Stars beat the Colorado Avalanche 5-3 in Game 2 on Thursday night to even the second-round Western Conference series.

Luka Doncic bounced back with 29 points, 10 rebounds and seven assists to help the Dallas Mavericks beat the Oklahoma City Thunder 119-110 on Thursday night and even the Western Conference semifinals at one win apiece.

Dallas police are examining security camera footage while detectives investigate.

The bill stalled earlier this week after senators from Virginia and Maryland objected to a provision that would allow an additional 10 flights a day to and from Ronald Reagan Washington National Airport.

Over the past several months, the CBS News Texas I-Team has reported on solar panel horror stories. This time, we set out to find a success story.

"I just jumped up and went woo-hoo!"
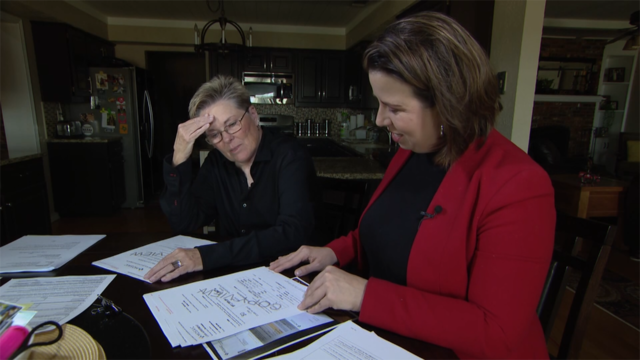
A Garland woman was surprised when she received a $97,000 bill for solar panels she doesn't have.

In a statement, Philips said it does not admit any wrongdoing but chose to settle "to end the uncertainty associated with litigation in the U.S."
A scammer a North Texas woman met on Instagram claimed to be a German cardiologist, and for months, the two messaged back and forth, building what she thought was a true relationship.

The bill stalled earlier this week after senators from Virginia and Maryland objected to a provision that would allow an additional 10 flights a day to and from Ronald Reagan Washington National Airport.

The Biden administration announced a new regulation designed to allow immigration officials to deport migrants ineligible for U.S. asylum earlier in the process.

Stormy Daniels gave defiant testimony Thursday as the defense accused her of fabricating details of the alleged sexual encounter between her and former President Donald Trump.

Greene's move marked a reversal from a day earlier, when the Georgia Republican appeared to retreat from her threat to trigger a vote to remove Johnson as speaker.

Stormy Daniels was called to the witness stand to testify at former President Donald Trump's trial in New York on Tuesday.

Over the past several months, the CBS News Texas I-Team has reported on solar panel horror stories. This time, we set out to find a success story.

Self-driving 18-wheelers have longtime truckers worried about their livelihood and others concerned that the technology needs more testing to make sure the public is safe.

McDonald's concept restaurant CosMc's has taken its drink-focused menu to Dallas for its second-ever location.

With the country on the cusp of greeting the return of spring, a warm-weather treat is once again available for free for a limited time only.

Kelli and Michael Regan were looking for a new dog. The breeder they found online asked them to pay with gift cards.

Panera is phasing out a highly caffeinated selection of lemonade beverages that's at the center of several lawsuits.

Steward Health Care, the struggling hospital group that owns hospitals in Massachusetts, Texas, Florida and other states, announced Monday that it is filing for bankruptcy.

The Texas dairy worker infected by H5N1 "did not disclose the name of their workplace," frustrating investigators.

A North Texas mother partnered with the Texas Health Resources Foundation to provide a potentially life-saving tool to at-risk pregnant and postpartum moms.

Plaintiffs have three months to vote on whether to approve a proposed legal settlement that would resolve nearly all talc lawsuits.

Within hours of the vote, the U.S. Chamber of Commerce announced it would sue to block the ban. Dallas employment attorney Rogge Dunn predicts employees will ultimately win this battle.

The closure affects both Dom's locations in Chicago, and all 33 Foxtrot stores in Chicago, Texas, and the Washington D.C. area.
Texas law SB 14 prohibits drug and surgical "gender transition" interventions for minors.

The projects are expected to create at least 17,000 construction jobs and 4,500 manufacturing jobs.

After more than 40 years in business, 99 Cents Only Stores, a discount chain, announced on Thursday that it will close all 371 of its locations and cease operations.

Dallas-Fort Worth hockey fans are searching for anything and everything related to the Dallas Stars and the Stanley Cup Playoffs.

Dallas Trinity FC will play at the Cotton Bowl when the season begins in August.

The Olympic flame arrived in France aboard a 19th century tall ship to kick off a 7,500-mile journey to the Paris Summer Games.

Another professional women's sport is coming to town.

Stars goalie Jake Oettinger stopped 22 shots, ending his six-game streak of allowing two goals or less.

This will be the first baby for Hailey and Justin Beiber, who announced their pregnancy after more than five years of marriage.

Traveonna Mays turned herself into the Denton jail Thursday on a charge of injury to a child.

'Bob Hearts Abishola', the acclaimed comedy, is signing off after its fifth season on CBS.

Bernard Hill died Sunday at 79. The actor was known for his roles in "Lord of the Rings" and "Titanic."

"Sunday Morning" has an exclusive behind-the-scenes look at the creation of the country singer's first post-stroke song, "Where That Came From," which blends art with artificial intelligence in a recording that captures Travis' country heart.

Amazon is adding a new way to deliver ads through Prime Video. If you are in the ad-supported tier, Prime Video will start showing ads when you hit pause. It's part of the new interactive ad format, but you can avoid the commercials completely by paying an additional price per month.

There is a noticeable shift in post-grad choices for many high schoolers this year. In fact, many are embracing alternative routes as opposed to traditional college paths. And there's a surge of young adults entering trades or immediately starting their careers after high school.
An Australian study discovered blood tests can show changes in the level of two different antibodies, and those changes can identify which children will likely outgrow a peanut allergy without clinical intervention.

The Reauthorization Act would provide $105 billion for the Federal Aviation Administration and $733 million for the National Transportation Safety Board. The bill now heads to the House.
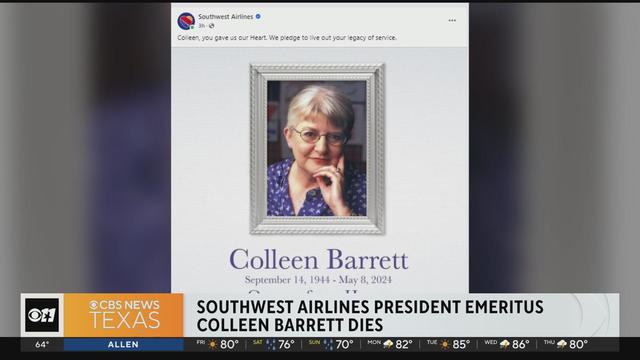
Southwest Airlines is mourning a woman that they call the heart and soul of their airline. Colleen Barrett has died at 79. Shee was considered instrumental in the carrier's early days, helping to bring about their love culture.

A storm chaser not only captured a massive tornado touching down in Hawley, Texas on Thursday but ended up rescuing a family of four whose home was destroyed by it.

Dallas artist Roberto Marquez traveled to the Rafah Crossing in Egypt, the U.S. capital and will attend this weekend's statewide protest in Austin.

On Friday, hundreds of thousands of fans gathered outside and all around Globe Life Field in Arlington to celebrate the Texas Rangers historical World Series win!

Babies in the neonatal intensive care unit at several Texas Health hospitals were dressed in creative costumes for Halloween.

Is that the smell of cotton candy, beignets and brisket wafting over Fair Park? It sure is, and we are here for it!